Blog
All the latest info and insights from the Akka team
Featured
Go Slow to Go Fast
An agentic systems platform enables a governance-first approach to agentic AI. Global CAIO of Manulife, Jodie Wallis, and Tyler Jewell, CEO of Akka, discuss what it means to go slow to go fast.
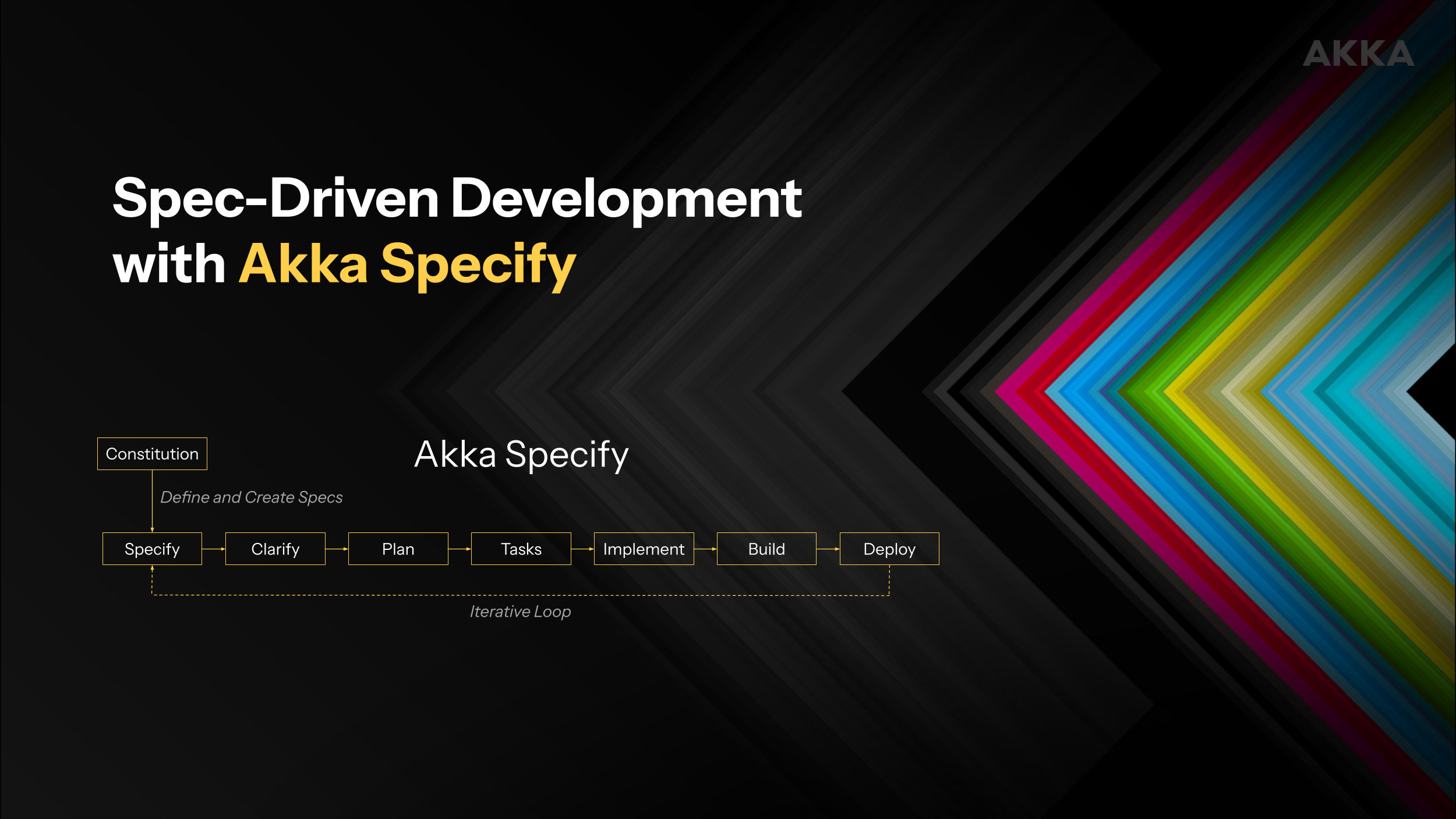
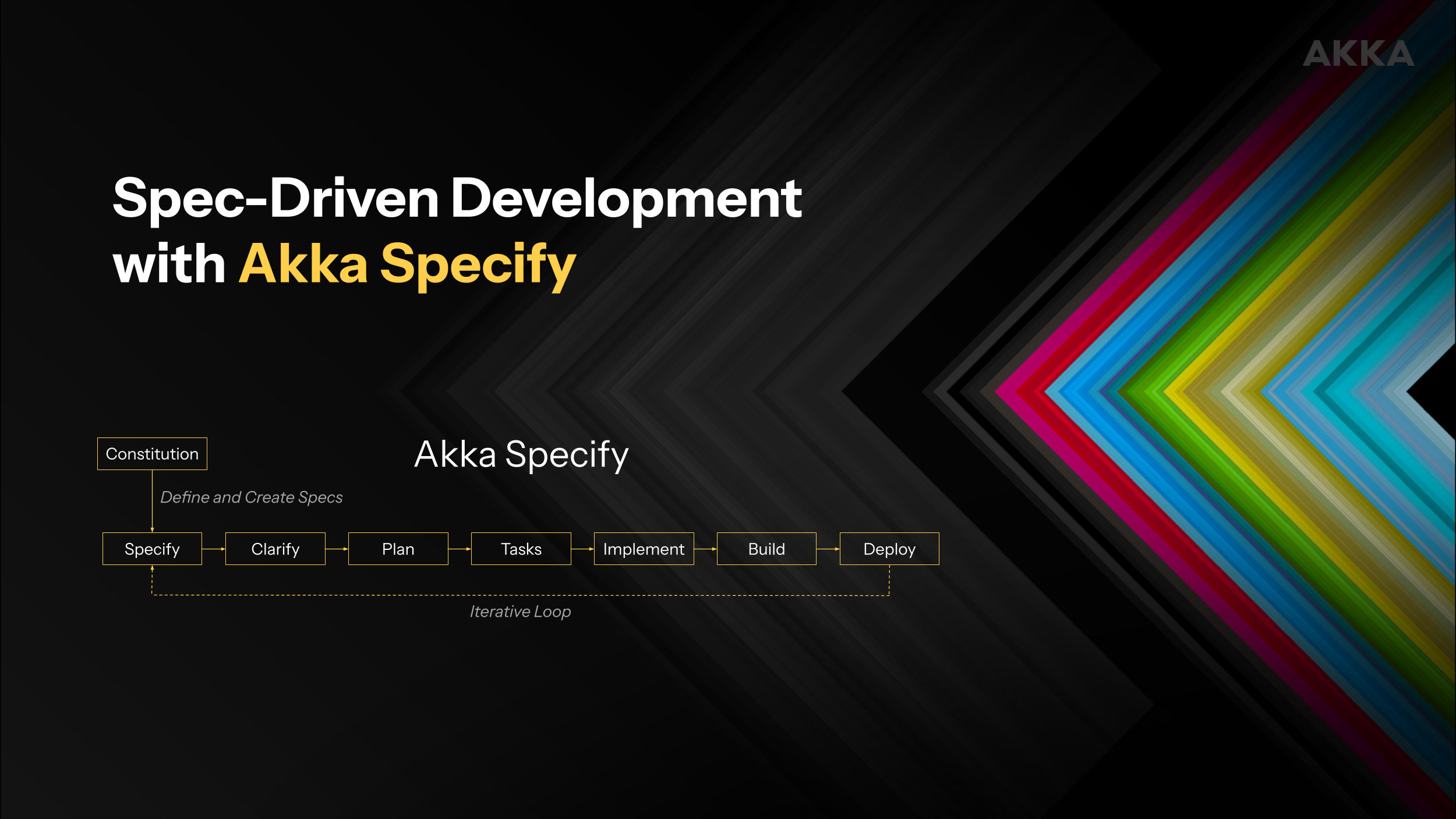
Introducing Akka Specify
Akka Specify provides SDD utilities to design, build, test, deploy and manage agentic AI systems through prompting from within your favorite AI assist tool. No coding, no IDE required.
Manulife Selects Akka to Operationalize Agentic AI within its Enterprise AI Platform
Akka to provide Manulife a secure and scalable software foundation to build hundreds of trusted AI-powered business applications.